
When setting up a new domain or updating an existing one, or if you’re looking to enhance email security, it’s essential to have a strategy and procedure in place ensure your domain remains secure. Over several years, I’ve developed a set of guidelines to provide a solid foundation for implementing domain security effectively.
All domains whether it sends mail or not should have an SPF, DKIM or DMARC There is never a good reason not to have SPF, DKIM or DMARC.
SPF (Sender Policy Framework):
- General Rule: An SPF record should conform to a maximum of 10 lookups.
- DMARC Compatibility: An SPF record, in conjunction with DMARC, should end in
~all. - Non-Emailing Domains: An SPF record for a domain from which no emails are sent should be
v=spf1 -all
DKIM (DomainKeys Identified Mail):
- Key Strength: DKIM keys must be at least 2048 bits.
- Non-Mail Domains: A non-mail domain should have a DKIM key of
"v=DKIM1; p=".
DMARC (Domain-based Message Authentication, Reporting, and Conformance):
- Policy Setting: DMARC should be set to
p=reject - DKIM Alignment: If possible, DKIM Strict alignment should be set to
adkim=s. - SPF Alignment: If possible, SPF Strict alignment should be set to
aspf=s. - Non-Mail Settings: A non-mail DMARC should conform to
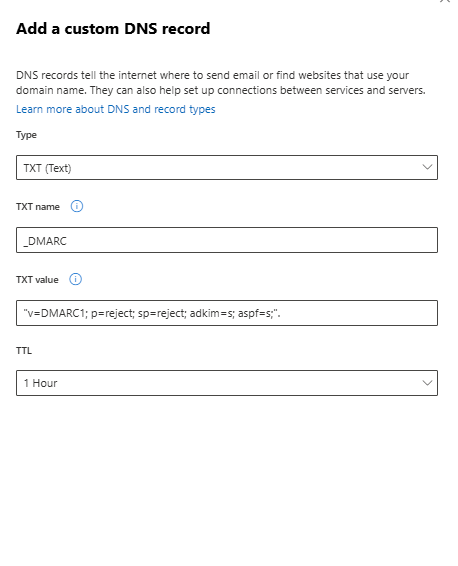
"v=DMARC1; p=reject; sp=reject; adkim=s; aspf=s;". - Specific Domain Setting: The
onmicrosoft.comdomain should also have a DMARC of"v=DMARC1; p=reject; sp=reject; adkim=s; aspf=s;".
You can do this by going to portal.office.com –> Settings –> Domains –> Click on your onmicrosoft domain and add a custom record.
MX (Mail Exchange) Records:
- Non-mail\Parked Domains: A domain from which no emails are sent should have an MX record with a value of
"0".
Network/Security:
- SMTP AUTH Deprecation: Be aware that SMTP AUTH is being phased out.
- Port 25: Should be closed on the internal network for clients. If you use port 25 for printers or servers this should be in a different VLAN
- TLS (Transport Layer Security): Communication should always occur over TLS.
- TLS Version: TLS must always be version 1.2 or higher. (Microsoft Exchange does not support 1.1 or 1.0)
Exchange Online:
- Connector Usage: Connector should only be used for tools such as Exclaimer,On prem exchange,etc
- TLS : Dane Should be enabled in the Office 365 tenant.
Domain
- DNSSEC should always be enabled in de DNS provider
Below is an example how a non-domain/parked domain should look like
Non-Mail (Sub)Domain DNS Configuration:
MX Record (Mail Exchange):
Name: Domain Name
Priority: 0
TTL (Time to Live): 600 seconds
Type: MX
Data: 0
SPF Record (Sender Policy Framework):
Name: Domain Name
Priority: 0
TTL: 600 seconds
Type: TXT
Data: v=spf1 -all
DKIM Record (DomainKeys Identified Mail):
Name: *._domainkey.<domain name> (Ensure this is correctly autofilled if applicable)
Priority: 0
TTL: 600 seconds
Type: TXT
Data: v=DKIM1; p=
DMARC Record
Name: _dmarc.<domain name> (Ensure this is correctly autofilled if applicable)
Priority: 0
TTL: 600 seconds
Type: TXT
Data: v=DMARC1; p=reject; sp=reject; adkim=s; aspf=s;
I hope this helps you with establishing a solid e-mail security baseline. The following tools can be useful to use when testing and troubleshooting your email security protocols.
https://www.internet.nl (Email security checks)
Subdomain Finder – C99.nl (Subdomain checker)
MX Lookup Tool – Check your DNS MX Records online – MxToolbox (Tool to check everything DNS and email related)
